LTE 初始附着过程中的NAS层安全流程

LTE 初始附着过程中的NAS层安全流程
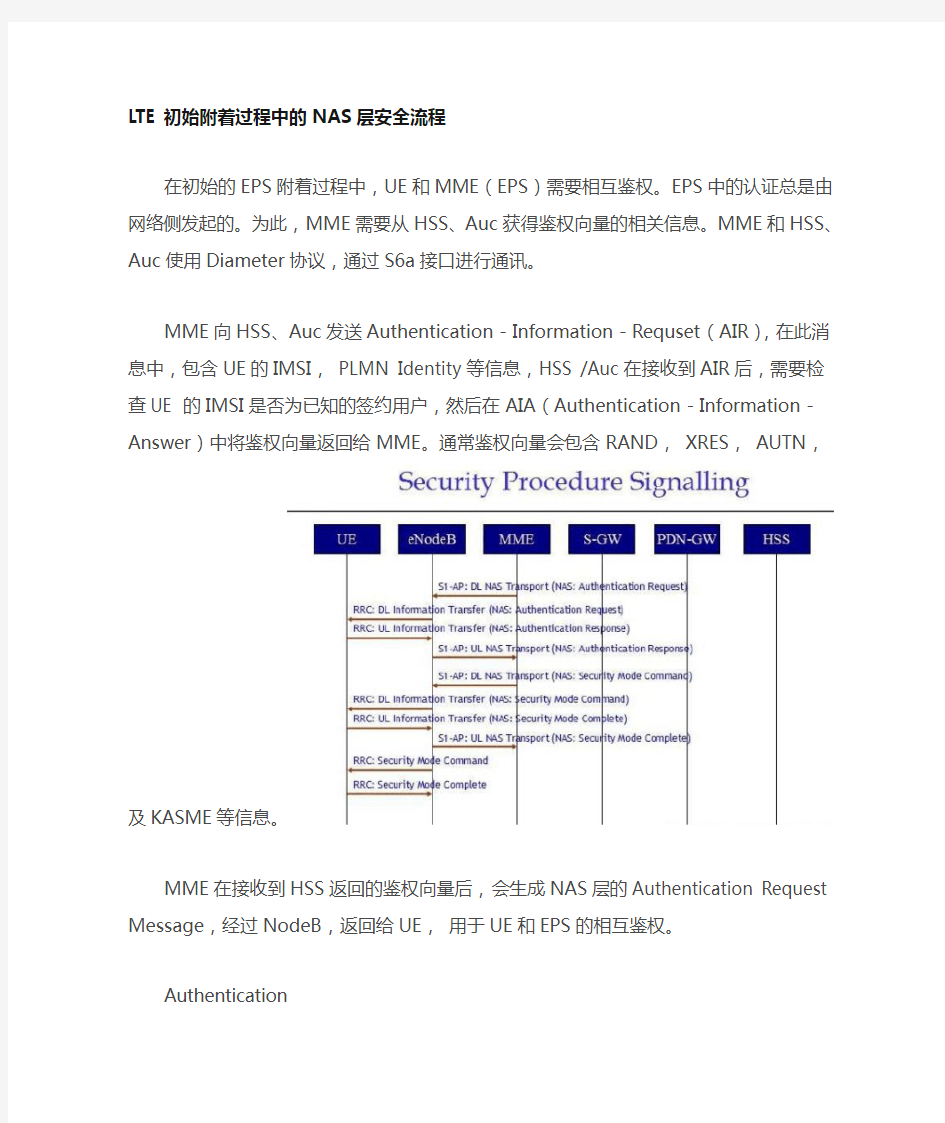
在初始的EPS附着过程中,UE和MME(EPS)需要相互鉴权。EPS中的认证总是由网络侧发起的。为此,MME需要从HSS、Auc获得鉴权向量的相关信息。MME
和HSS、Auc使用Diameter协议,通过S6a接口进行通讯。
MME向HSS、Auc发送Authentication-Information-Requset(AIR),在此消息中,包含UE的IMSI, PLMN Identity等信息,HSS /Auc在接收到AIR后,需要检查UE 的IMSI是否为已知的签约用户,然后在AIA(Authentication-Information-Answer)中将鉴权向量返回给MME。通常鉴权向量会包含RAND,XRES, AUTN,及KASME等信息。
MME在接收到HSS返回的鉴权向量后,会生成NAS层的Authentication Request Message,经过NodeB,返回给UE,用于UE和EPS的相互鉴权。
Authentication
Request 26.504
Security header type [4 bits] = 0x0 [ 0 ]
Protocol Discriminator [4 bits] = 0x7 [ 7 ]
Message Type [8 bits] = 0x52 - Authentication Request [ 82 ]
Spare Half Octet [4 bits] = 0x0 [ 0 ]
NAS key set identifierASME
Type of security context flag [1 bit] = 0x0 [ 0 ]
ksi [3 bits] = 0x0 [ 0 ]
Authentication Parameter Rand
Authentication Parameter Rand =
0xA3DE0C6D363E30C364A4078F1BF8D577
Authentication Parameter AUTN
IE Length [8 bits] = 0x10 [ 16 ]
value = 0x6E323B36C46C5555A3DF0E6E323B6391
MME会在Downlink NASTransport消息中,将上面NAS层的鉴权请求发送到NodeB,由于此时UE到MME的S1连接还没有建立, MME还会在Downlink NAS Transport 中包含一个唯一的 MME_UE_S1APID,这样,NodeB就会为此UE建立起相应的
S1-MME连接。同时,NodeB会通过Downlink Information Transfer消息将EPS 的鉴权请求发送给相应的UE。
UE在接收到MME发送过来的NAS层的AUR消息后,启动相应的AKA鉴权过程, LTE 首先对通过对AUTH的检查来对网络侧进行鉴权,通过后,UE生成相应的Res和IK, CK通过NAS层的AUA消息返回到MME,进行UE的鉴权。AUA消息作为ULInformationTransfer消息中的DedicatedInfoNAS信元通过DCCH信道发送给NodeB ,NodeB通过UplinkInformationTransfer消息将AUA转发给相应的MME。
Authentication
Response Security header type [4 bits] = 0x0 [ 0 ]
Protocol Discriminator [4 bits] = 0x7 [ 7 ]
Message Type [8 bits] = 0x53 - Authentication Response [ 83 ]
Authentication response parameter
IE Length [8 bits] = 0x8 [ 8 ]
Authentication response parameter information = 0xA3DF0E6E323B36C4
MME在成功对UE进行鉴权以后,就会根据UE上报上来的安全能力(UE在AttachRequest中的DedicatedInfoNAS中指明)来选择合适的算法进行NAS层的加密和信令完整性保护。MME会通过NAS Security Mode Command 消息将选中的算法传送给UE,同时MME也会将接收到的UE安全能力返回给UE。UE对NAS Security Mode Command 消息做完整性保护。
Security Mode Command PDU
[1]Security header type [4 bits] = 0x0 [ 0 ]
Protocol Discriminator [4 bits] = 0x7 [ 7 ]
Message Type [8 bits] = 0x5D - Security Mode Command [ 93 ]
Selected NAS security algorithms
Spare Bits [1 bit] = 0x0 [ 0 ]
Type of ciphering algorithm [3 bits] = 0x0 [ 0 ]
Spare Padding [1 bit] = 0x0 [ 0 ]
Type of integrity protection algorithm [3 bits] = 0x1 [ 1 ]
Spare Half Octet [4 bits] = 0x0 [ 0 ]
NAS key set identifierASME
Type of security context flag [1 bit] = 0x0 [ 0 ]
ksi [3 bits] = 0x0 [ 0 ]
Replayed UE security capabilities
IE Length [8 bits] = 0x2 [ 2 ]
eea0_128 [1 bit] = 0x1 [ 1 ]
eea1_128 [1 bit] = 0x1 [ 1 ]
eea2_128 [1 bit] = 0x0 [ 0 ]
eea3 [1 bit] = 0x0 [ 0 ]
eea4 [1 bit] = 0x0 [ 0 ]
eea5 [1 bit] = 0x0 [ 0 ]
eea6 [1 bit] = 0x0 [ 0 ]
eea7 [1 bit] = 0x0 [ 0 ]
Spare Bits [1 bit] = 0x1 [ 1 ]
eia1_128 [1 bit] = 0x1 [ 1 ]
eia2_128 [1 bit] = 0x0 [ 0 ]
eia3 [1 bit] = 0x0 [ 0 ]
eia4 [1 bit] = 0x0 [ 0 ]
eia5 [1 bit] = 0x0 [ 0 ]
eia6 [1 bit] = 0x0 [ 0 ]
eia7 [1 bit] = 0x0 [ 0 ]
UE接收到NodeB转发过来的NAS层的 Security Mode Command消息后,首先验证其中的UE安全能力与自己早先上报给MME的一致,然后根据NAS Security ModeCommand中选中的算法计算相应的密钥,并生成 NAS SecurityModeComplete 消息,对之进行完整性保护,发送给MME。
此时,可以认为NAS层的安全性已经激活, UE和NodeB可以进行安全的NAS层对话。
Security Mode Complete PDU
Security header type [4 bits] = 0x0 [ 0 ]
Protocol Discriminator [4 bits] = 0x7 [ 7 ]
Message Type [8 bits] = 0x5E - Security Mode Complete [ 94 ]
